
The data includes information about credit and debit cardholders and is being sold on the dark web
The data, which is in the form of a data dump, appears to have been leaked through a compromised server of payments company Juspay
Names of issuing bank, expiry date, masked credit/debit card numbers, names, customer ID and merchant account ID have been leaked among several other details
In what is seemingly India’s biggest data leak in recent times, in terms of the number of users affected, the data of 10 Cr cardholders has been leaked on the dark web.
The leaked data, which is in the form of a data dump, appears to have been leaked through a compromised server of Bengaluru-headquartered mobile payment solutions company Juspay.
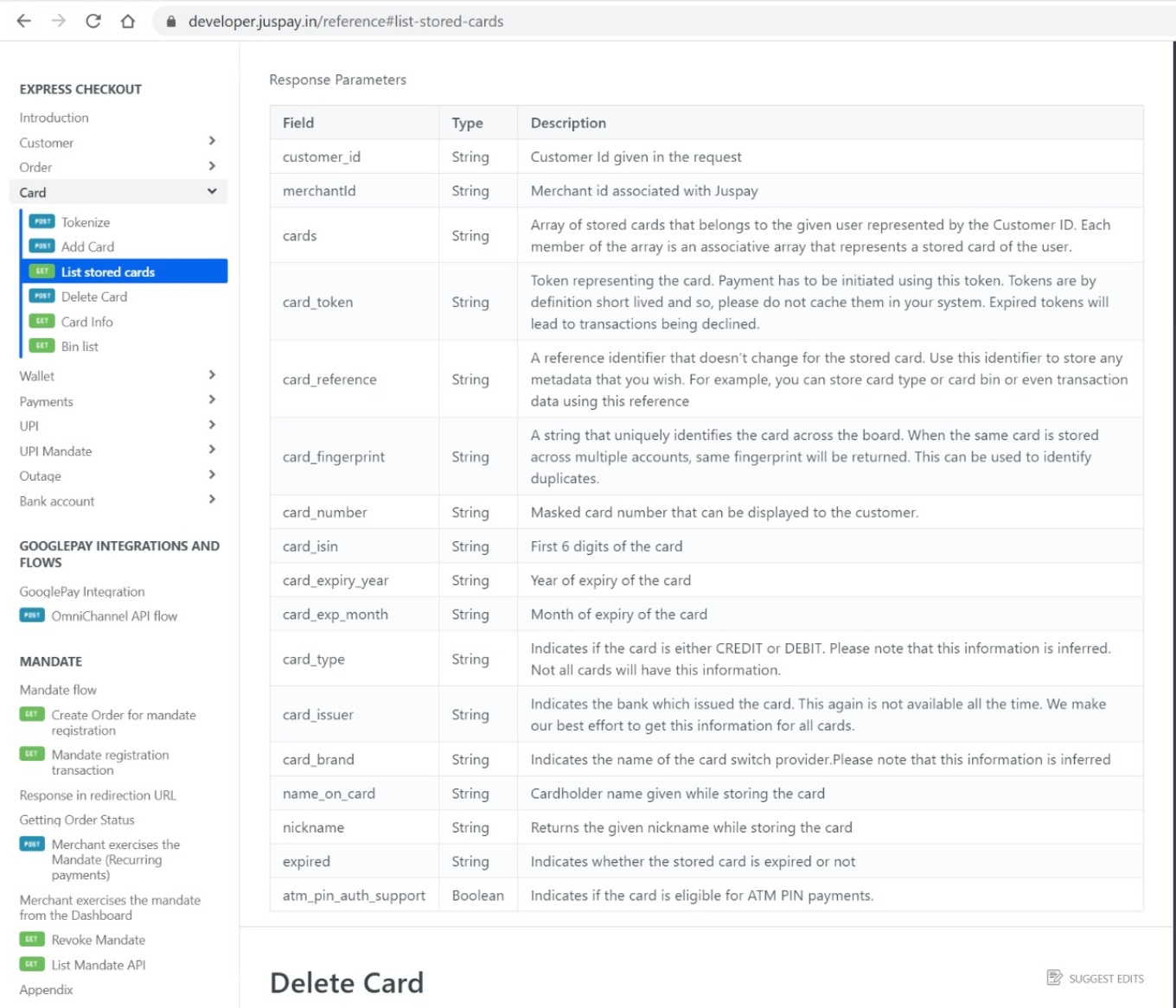
Screenshots of the leaked database, accessed by Inc42, reveal that it contains sensitive information. This includes a user’s card brand (VISA/Mastercard), card expiry date, the last four digits of the card, the masked card number, the type of card (credit/debit), the name on the card, card fingerprint, card ISIN, customer ID and merchant account ID, among several other details. In all, over 16 fields of data relating to their payment cards have been leaked for at least 2 Cr users, as conceded by Juspay, a subset of the total number of user records (10 Cr) that have been leaked.
A brief description of what each of these data fields means can be found in the image below.
Another subset of the leaked database contains users’ phone numbers and email addresses.
The leaked payment information has been masked in places to reveal only partial copies of card numbers. While this reduces the possibilities of a financial scam, resourceful hackers could still use the information to launch phishing scams to induce victims to hand over their card information.
Cybersecurity researcher Rajshekhar Rajaharia, who first alerted Inc42 of this development, said that the data was being sold on the dark web for an undisclosed amount. Rajaharia added that such data could fetch a hacker a handsome amount of money on dark web marketplaces.
It is worth noting that the standards laid down in PCI DSS (Payment Card Industry Data Security Standard) have been followed by Juspay in storing users’ card information. However, Rajaharia felt that if the hacker can find out the algorithm used to generate the card fingerprint, then he will be able to decrypt the masked card number.
Juspay Responds On Data Leak
Juspay offers a software development kit (SDK) for app makers to integrate its services. It counts major Indian and international tech companies such as Amazon, Airtel, Swiggy, Vodafone, Uber, Cred, Ola and Flipkart among its clients. Its solution powers the payment gateways for these companies and Juspay claims that it processes over 2 Mn transactions per day.
Responding to Inc42‘s queries, a Juspay spokesperson said, “On August 18, 2020, an unauthorised attempt on our servers was detected and terminated when in progress. No card numbers, financial credentials or transaction data were compromised. Some data records containing non-anonymised, plain-text email and phone numbers were compromised, which form a fraction of the 10 Cr data records.”
The spokesperson added that the metadata, mostly anonymised, for 10 Cr processed transactions was leaked, with a subset containing email and mobile information. Further, the company said that full credit or debit card numbers were never accessed
“The masked card data (which is not sensitive) has 2 Cr user records. Our card vault, in a different PCI-compliant system with encrypted card data, was never accessed,” he said.
The spokesperson added that hackers from the infamous ‘ShinyHunters’ group had gained access to one of Juspay’s developer keys and was spawning new computation servers in the developer account and trying to gain access to any accessible data. The spokesperson claimed that the masked card numbers that have been leaked, are not considered sensitive as per compliance. He also said that the “few” phone numbers and email addresses that have been leaked have dummy values.
According to the spokesperson, Juspay intimated its merchant partners about the data leak the very same day and upon identifying gaps, strengthened some of its cybersecurity measures.
Data Leaks Haunt Startups
The first murmurs of this massive data leak had come in October 2020, when US-based cybersecurity intelligence firm Cyble had approached Juspay, alerting it about the data breach. However, it has been alleged that Cyble also pitched its services to the Indian startup and said the data leak report would not be made public if Juspay agreed to sign up as a client. Further, Juspay is reportedly said to have taken up the offer, following which the report was buried.
This practice by Cyble was first reported in November 2020 by The Ken. Cyble was reported to have approached Indian online grocery unicorn Bigbasket with a similar offer in October. In what is alleged to be extortion by some observers, Cyble is believed to have asked Bigbasket to pay $80,000 for its cybersecurity services, and to bury the news about the data leak.
BigBasket declined to pay and Cyble was the first to report on the company’s data breach, which was subsequently re-reported by several Indian digital media outlets. While BigBasket chose to report to the authorities that Cyble had demanded “ransom” from it, the American company denied the same in an update to its blog.
As for the recently leaked data from Juspay, Rajaharia has independently confirmed that the information for at least some users is genuine. The fact that it’s in the form of a data dump rules out the possibility of the data being leaked through an API (Application Programming Interface). Instead, it seems like the hacker was able to gain access to Juspay’s server.

Meanwhile, according to a recent report on Security Affairs, the threat actor purportedly selling the data of Juspay users is in possession of 36.9 Cr stolen user records obtained from 26 companies, which includes the data of 2 Cr BigBasket users leaked in November. The said hacker also holds stolen data of 80 Lakh users on Indian classifieds company Clickindia, according to the report.

India’s Poor Cybersecurity Track Record
This development comes just as 2020 has come to a close, a year when India witnessed a rapid rise in phishing and social engineering, ransomware, distributed denial of service or DDoS, and several other kinds of cyber attacks on its companies. According to the Ministry of Electronics and Information Technology (MeitY), Indian citizens, commercial and legal entities faced 7 Lakh cyber attacks till August 2020 alone, nearly double the number of cyber attacks in 2019 — 3.94 Lakh.
Besides BigBasket, Google-backed hyperlocal delivery platform Dunzo, restaurant chain owner Haldirams, edtech platform Edureka, online travel marketplace RailYatri and even the personal website of Prime Minister Narendra Modi suffered data breaches in 2020, with the data on some of these websites being subsequently leaked on the dark web where it was available for purchase.
Cybersecurity experts Inc42 spoke to, were of the opinion that the rapid rise in cyber attacks on Indian companies can be attributed to the shift to work from home (WFH) for most companies amid the Covid-19 pandemic. Moreover, Indian’s geopolitical tensions with its neighbours China and Pakistan in the year gone by may also be to blame for the spate of cyber attacks.
Update Notes
2:11 PM: Juspay’s response was added.
4:25 PM: Based on further information from Juspay, minor additions made to the story in relevant places.
11 PM: We have updated the headline to reflect the facts more accurately.























 Ad-lite browsing experience
Ad-lite browsing experience