SUMMARY
Paytm CEO Vijay Shekhar Sharma Tweeted It Was Being Done On NPCI's request
The Android app Of Paytm has been asking users who have modified or rooted their devices for administrative access called root access, as per a Medianama report.
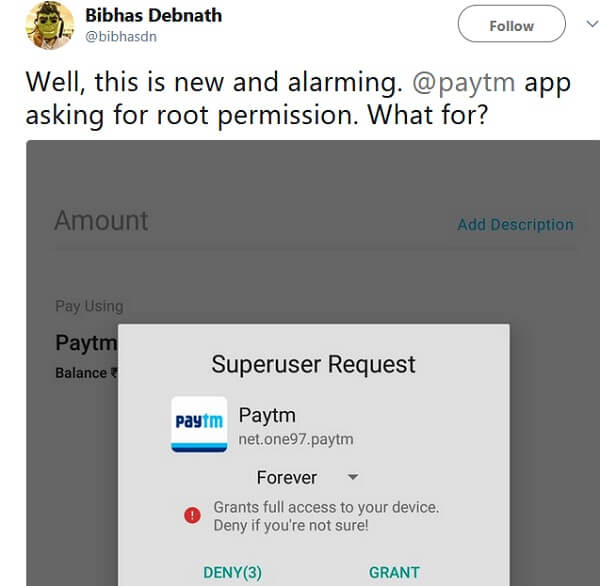
This issue was first brought to light by a Twitter user Bibhas Debnath, who shared a screenshot of the request prompt.
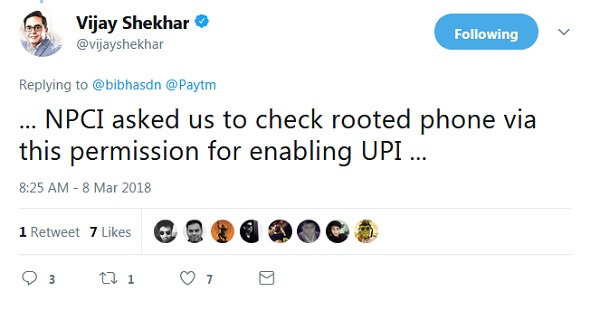
This tweet gained a lot of attention, forcing even Paytm founder and CEO Vijay Shekhar Sharma to respond that the National Payments Corporation of India (NPCI) had asked the app maker to check for rooted devices before enabling access to UPI payments.
Understanding Root Access
If a user allows the app to gain administrative access also known as root access or superuser access it will, in theory, have complete control over the device.
Rooting allows users to gain privileged control of their Android devices, thus removing any barriers to modification and tweaking of the device’s software. Once a device is rooted it can be used to modify the device’s behaviour. Normally this is restricted to the user himself. However certain apps though can be given this privilege that allows them complete access to the device and its system software.
But the question raised by the Twitter user is why does Paytm need this? Because with root access, the Paytm app can do anything it wants on the phone, read a user’s messages or go through his call history. Even though Paytm has pointed out that it doesn’t intend to do any of this but still it raises concerns about the privacy of the user, the security of the device, and of a possible threat from hackers.
Also, what makes it more absurd is that the app does not need any root permissions to perform its operations effectively. More so with Vijay Shekhar Sharma stating that it is being done on NPCI’s behest has further raised eyebrows.
Paytm did not comment on the query sent to them.
Given the rise in threat from malware and hackers, it is natural that Paytm app asking for root access on Android phones has raised concerns as it does lead to a possibility of breach in cyber security, even though the app has indicated it would not misuse the privilege awarded by root access.






























 Ad-lite browsing experience
Ad-lite browsing experience