The data has been leaked by the same hacker who earlier this month, had leaked the data of 10 Cr digital payments transactions from the server of Juspay
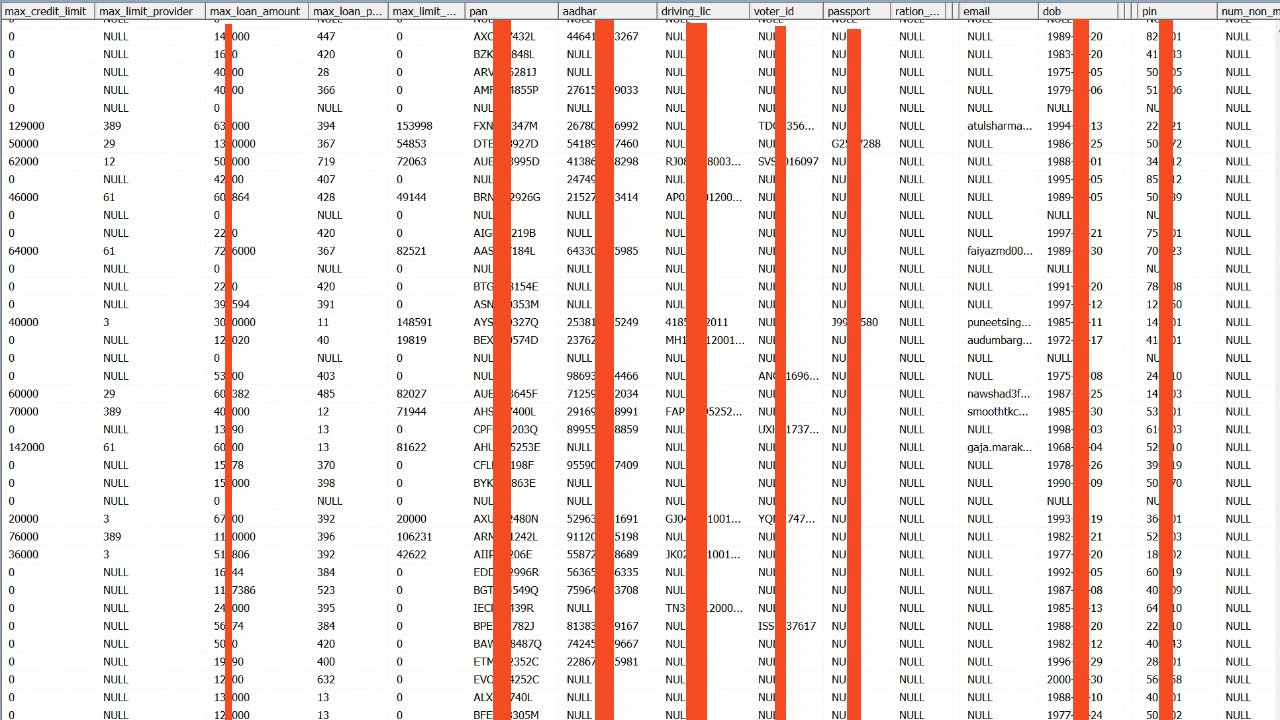
Chqbook’s leaked data contains users’ names, contact details, Aadhaar and PAN numbers, the maximum loan amount they had sought or obtained from the company
Chqbook is an Indian fintech startup and neobank for small businesses
Data of over 20 lakh credit score records with Chqbook, the Delhi NCR-based fintech startup, has been leaked on the dark web. The data breach is the handiwork of the hacking group ShinyHunters, which had leaked the data of 10 Cr digital payments transactions from Indian mobile payment solutions company Juspay’s server earlier this month.
While information about Chqbook’s data breach has been out in the public domain since late last month, the company had denied the occurrence of any data breach.
Data stolen from Chqbook is now available for free on the dark web and contains sensitive personal as well as personally identifiable information such as users’ names, email IDs, phone numbers, Aadhaar card and PAN numbers, the maximum loan amount they had sought or obtained from the company and their credit score reports and more.
It is worth noting that all the fields of data mentioned above aren’t provided for all users. Nevertheless, for several users, even their passport numbers, home addresses and date of birth (DOB) are mentioned in the leaked database.
Chqbook helps its users avail financial services such as credit cards, loans and insurance, among others. Founded in 2017 by Vipul Sharma, Rajat Kumar, Sachin Arora, and Mohit Goel, Chqbook says that its mission is to empower the segment that is massively underserved by traditional banks, to help drive financial inclusion. The company claims to have over 5 lakh users across 25 Indian cities.
According to cybersecurity researcher Rajshekhar Rajaharia, who alerted Inc42 of this development, the leaked database also contains information from 45 lakh METRO Cash & Carry Cards, the international B2B wholesaler. METRO Cash & Carry has been in India since 2003 and claims to be operating 25 wholesale distribution centres under the brand METRO Wholesale in 15 cities.
METRO Cash & Carry India’s core customers include small retailers and kirana stores, hotels, restaurants and caterers (HoReCa), corporates, SMEs, all types of offices, companies and institutions, as well as self-employed professionals. Only business customers are allowed to purchase at METRO, all of them duly registered and provided with customer registration cards.
In 2018, METRO had partnered with Chqbook for providing financial services to the wholesaler’s extensive SME and kirana ecosystem.
Last month, it was reported that a threat actor was in possession of 368.8 Mn user records obtained from 26 data breaches. Of these, five data breaches were of Indian companies, namely Juspay, Clickindia, WedMeGood, Chqbook and BigBasket. It was reported then that 1 Mn (10 lakh) Chqbook user records were in possession of the threat actor, who is understood to be a part of the infamous hacking group ShinyHunters. Now that number has swelled to 20 lakh. We couldn’t independently ascertain the authenticity of the leaked data.
Last month, when the leaked data was not available on the dark web, Chqbook, in a response to securityaffairs.co, had denied that any data breach had taken place. Inc42 has reached out to Chqbook with fresh queries about the recent data breach, screenshots of which have been accessed by us.
Meanwhile, earlier this month, Inc42 reported that the data of 3.25 lakh users of New Delhi-based Indian crypto exchange BuyUCoin had been leaked on the dark web by ShinyHunters. BuyUCoin initially denied the data breach and claimed that dummy data of just 200 users had been leaked. However, when confronted with proof shared by Rajaharia, who was himself an affected user, BuyUCoin issued another statement claiming that it was investigating any possible security lapses.
Update – January 27, 2021, 7:17 pm: Headline has been updated to reflect the details of the incident more accurately.

























 Ad-lite browsing experience
Ad-lite browsing experience