SUMMARY
Websites of certain Indian state governments and central agencies have extension links which direct users to porn and dating websites
These extension links, which are attached to the URLs of these government websites, can be found through a simple Google search with the right keywords
Cybersecurity experts felt that this could be the work of hackers looking to initiate large-scale phishing attacks
Vulnerabilities associated with the cybersecurity infrastructure of Indian companies and startups have already made the news several times in the past two years. More worryingly, this week, new threats associated with several Indian government websites have come to light, with their sitelink extensions (which take users to specific pages on a website) directing users to pornographic and dubious dating sites.
The websites in question are operated by Indian state governments and central agencies, and host pages that take users to pornographic websites and dating platforms. These pages can be found through a Google search with the right keywords. However, the redirect path for these porn and dating websites couldn’t be ascertained.
Mohit Kohli, founder of artificial intelligence (AI)-enabled cybersecurity company Foresiet, first spotted the anomaly in late December 2020 and alerted the Data Security Council of India (DSCI) and the Indian Computer Emergency Response Team (CERT-In), following which the bug was fixed for certain websites, particularly those with sitelink extensions to porn sites. However, as pointed out by Kohli and verified by Inc42, the issue persists for several websites run by state governments and central agencies, one of them being a website of the Uttar Pradesh legislative assembly.
Kohli felt this is the work of malicious hackers, as data from some of these government websites has been leaked on the dark web. Inc42 has accessed screenshots of the data leaked on the dark web. It includes login credentials such as user IDs and passwords. Although, it is unclear how the hacker collected the data or whether it pertains to the development being reported here.
Besides, the motivations for the hacker are unclear. Experts said attackers could be selling the data that has been siphoned off from this site, using them for more serious attacks, or the attack could be a means to soil the reputation of the Indian government.
Inc42 has reached out to the Data Security Council of India (DSCI), an industry body on data protection in India, set up by NASSCOM. We have also intimated the Indian Computer Emergency Response Team (CERT-In) about this development. This story will be updated if either body responds to our queries.
Why Indian Government Websites Are Vulnerable
This is not the first instance of government websites redirecting users to dubious sites. In 2019, the Goa government’s website was redirecting users to a porn site for several hours. Foresiet’s Kohli added that Indian government websites, by virtue of being hosted on Liferay, an open-source enterprise-grade web development platform, leave themselves vulnerable to certain associated risks.
“When an open relay is enabled on a website, attackers can redirect users to another website, which works as bait for phishing attacks. Users who visit the dating website would feel compelled to sign up and provide their details to avail the service. By doing this, they would hand over their personal information to the attacker who is operating the site,” said Kohli.
Independent cybersecurity researcher Rajshekhar Rajaharia studied the Uttar Pradesh legislative assembly website. According to him, the bug has occurred because the developer contracted to build the state’s website, used the server provided by the National Informatics Centre (NIC) to also build another website — in this case, a dating website.
“This would constitute a violation of the state government’s contract/arrangement with the developer. Essentially, the developer has used a server provided to him by the government for his personal project,” the expert added.
Are Hackers Looking To Target New Internet Users?
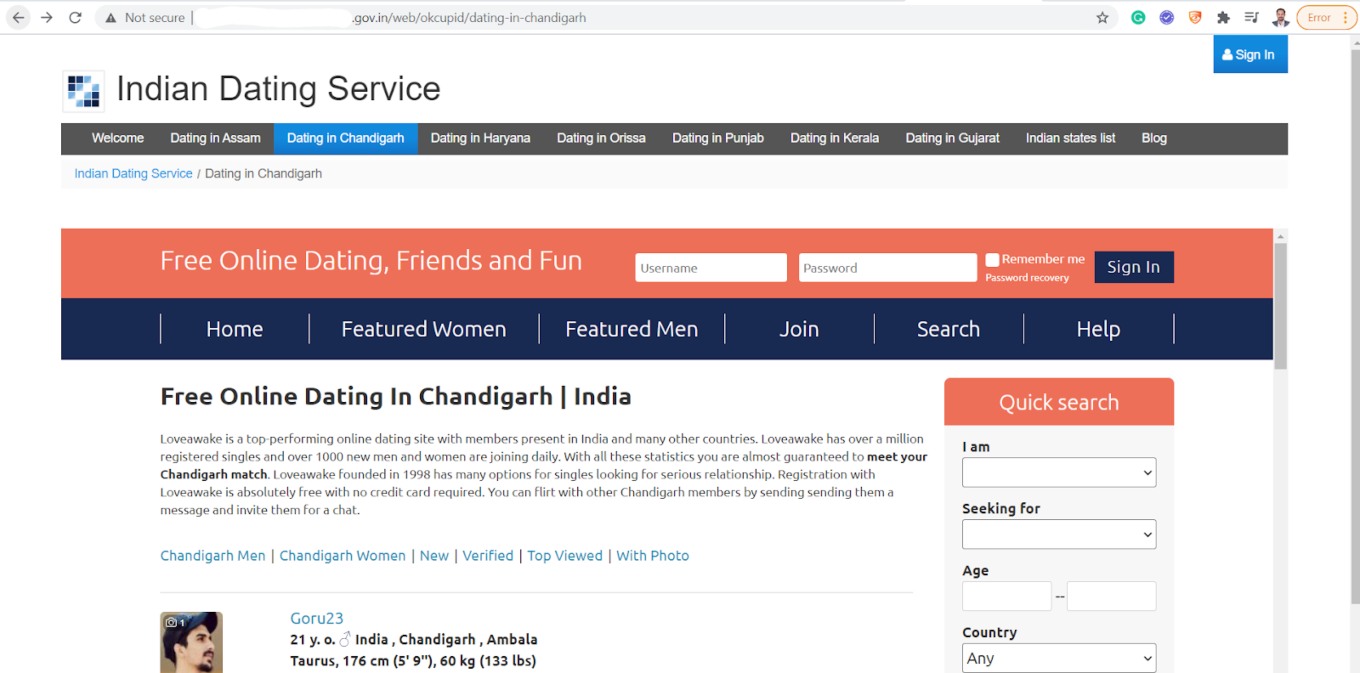
It is worth noting that the said UP government website is classified as ‘Not Secure’ by the Google Chrome browser. About the ‘Not Secure’ security flag, Google Chrome says, “ Proceed with caution. Something is severely wrong with the privacy of this site’s connection. Someone might be able to see the information you send or get through this site.”
We could see the ‘Secure’ security symbol for websites of several other state governments in India, which indicates that the ‘Not Secure’ flag for this particular website is indeed an anomaly.
Cybersecurity expert Viney Kumar pointed out that the UP government website hasn’t been built on SSL, as depicted by its web address, which doesn’t begin with ‘HTTPS’ but ‘HTTP’. “In HTTPS, the communication protocol is encrypted using Transport Layer Security or, formerly, Secure Sockets Layer. So, this is a big miss from the web developer and if it has been done intentionally on a government website then it may turn out to be a crime for providing the government with an unsafe website. This gives any hacker the space to enter the web server and then employ cross-site scripting (XSS), code injection, and perform defacement,” he said.
Further, several details on the homepage of the dating website don’t match up. The header reads ‘Indian Dating Service’, with various sub-heads below it, reading: ‘Dating in Assam’, ‘Dating in Chandigarh’, ‘Dating in Haryana’, and so on.
However, the footer of the homepage talks about Loveawake.com, a dating service apparently operational since 1998.
Shomiron Das Gupta, founder and CEO of cybersecurity firm Netmonastery felt that a fake dating website that mimics an actual one can serve as a honeypot for unsuspecting users, luring victims who may lack understanding of internet safety for more severe attacks. Das Gupta added that plots involving romantic themes through online dating are among the most prevalent for large-scale phishing attacks.
“The user is redirected to a dating page where they can follow instructions on how to register as an exclusive member to avail premium benefits. If the target falls prey to it, he has already exchanged critical information like name, phone number, email id, perhaps even credit card information, among other financial or personal credentials etc.,” he said.